
This is a CRAZY and juicy attack! It is definitely something you should aware of especially if you’re going to be asked about serious threats to large organizations!
SolarWinds is a sofware company that is utilized across all kinds of organizations of all sizes. I’ve even pen-tested some of their software(s) during internal pen tests I’ve worked on.
If you weren’t aware, supposedly Russian hackers compromised SolarWinds update distribution site and poisoned an update. Thus in turn, breaching thousands of organizations who installed the malicious update.

Remember that FireEye was breached a few days ago? If not I posted about it HERE
They’re now claiming that SolarWinds was how their APT got their foothold into their network (Source HERE)
Imagine poisoning the supply chain and finding out you breached multiple government agencies AND the biggest cyber security firm (at least in the US)? Must feel pretty successful.
These supply chain attacks are fairly rare but are especially damaging! They are in the top 5 ways you can truly compromise some of the largest organizations.
This is definitely a story you should keep up with and note for your next job interview! Just like target, I think that this incident will be talked about for a long time.
One thing I found especially interesting (and unbelievable) were the screenshots below that show that Solarwinds specifically told their customers to add their Solarwinds installations to their Anti-Virus’s exception list! OMG. Don’t worry, they have since deleted this recommendation from their site!

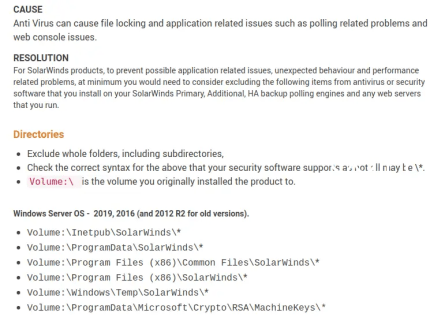
Source for this screenshots is HERE
SANS Article on this diaster HERE
Here is a great Vice article on this diaster HERE
More information about what a Supply Chain Attack is HERE
